enterprise file sync and share (EFSS)
What is enterprise file sync and share?
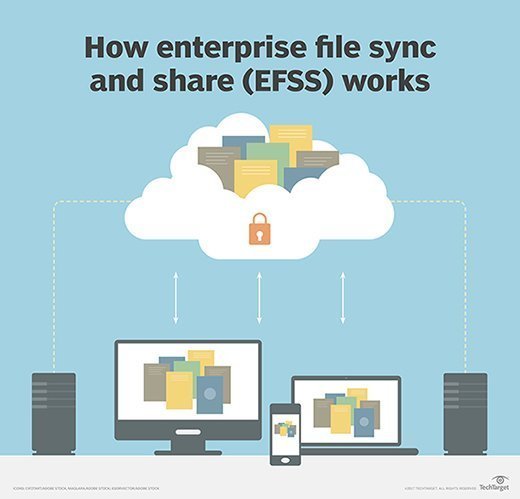
Enterprise file sync and share (EFSS) is a service that allows users to save files in cloud or on-premises storage and then access them on desktop and mobile devices.
How does EFSS work?
Enterprise file-sharing tools let users securely share documents, photos, videos and more across multiple devices and people. They use file synchronization, or copying, to store files in an approved data repository where they can be accessed remotely by employees from PCs, tablets or smartphones that support the EFSS product.
Why use an EFSS service?
Organizations can use an EFSS service to improve content management, collaboration and secure employee file sharing. EFSS services include live commenting, document version tracking and workflow process management to help users store, edit, review and share files.
Organizations often adopt EFSS to deter employees from sharing corporate data via consumer-oriented public cloud file-sharing services outside IT's control. To that end, enterprise file-sharing products include security features such as multifactor authentication, single sign-on, data loss prevention, data encryption, containerization and tracking to protect enterprise data.
Still, not all EFSS offerings include encryption to protect data after it's transferred locally to a user's device or shared with a third party. Some EFSS services also let IT administrators set access policies that govern who can access certain content.
Features and benefits of EFSS
EFSS services can improve an organization's productivity and protect its files from security threats. Many different features come together in an EFSS service to support these benefits. Key features include the following:
- Live commenting. As workers create and edit content, live commenting lets them easily collaborate with co-workers in real time.
- Document version control. EFSS services save and track different versions of documents as employees edit them. This feature helps workers find up-to-date document versions and lets them compare current versions to original drafts.
- Integration with other business applications. EFSS tools can integrate with other applications, such as email, calendar and productivity, to optimize workflows.
- Workflow notifications. This feature alerts employees, often by email, of tasks that need their attention. For example, a content marketer may receive an automated email after their supervisor assigns them a new piece of content to work on.
- Encryption. EFSS service providers typically encrypt documents in their cloud storage, which can protect sensitive information from bad actors.
- Access control. EFSS systems offer access controls that let administrators limit sensitive information access to employees with special permissions. These security measures should reduce compliance and security risks.
EFSS and mobility
Organizations can deploy EFSS as a private or hybrid cloud service or on-premises software. With a cloud deployment, employees save files in the EFSS provider's cloud, and users with network connectivity access them remotely on a PC or mobile device. In most hybrid and on-premises deployments, the files remain in the company's data repository.
Enterprise file sharing became more critical as organizations embraced the need for employees to access their corporate files from multiple device types. The top EFSS providers have applications that allow users to access and edit files on PCs, smartphones and tablets and use file synchronization on the back-end server to update the file across all their devices.
Choosing an EFSS vendor
EFSS products include Axway's Syncplicity, Box, BlackBerry Workspaces, Citrix ShareFile, Dropbox Business, Egnyte, Google Drive, Kiteworks, Microsoft OneDrive and several others.
Organizations most often choose an EFSS product based on its cost, security capabilities, management controls, user productivity features and its ability to easily integrate with other tools and applications that the business already uses.
Although EFSS products usually offer secure file storage, synchronization and sharing capabilities, they each have standout features and benefits. For instance, Syncplicity offers relatively low pricing for organizations on a strict budget. Box, on the other hand, offers workflow automation features that let users design their workflows. BlackBerry Workspaces is known for its strong security features, namely its AES-certified 265-bit encryption and ransomware protection. And for organizations that need a digital workspace suite, ShareFile offers native integration with Citrix Workspace.
From EFSS to content collaboration
In step with the expanding capabilities of EFSS tools, Gartner, in 2017, changed the name of its Enterprise File Synchronization and Sharing Magic Quadrant to Content Collaboration Platforms. Over time, these products have moved beyond file synchronization and remote access features to include internal messaging, workflow management and data security capabilities. As organizations embrace hybrid workplaces and consumers demand stricter data privacy laws, experts expect the content collaboration market to grow.






