OTA update (over-the-air update)
What is an OTA update (over-the-air update)?
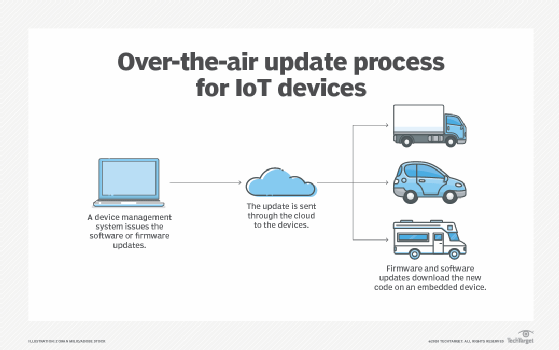
An over-the-air (OTA) update is the wireless delivery of new software, firmware or other data to mobile devices.
Wireless carriers and original equipment manufacturers (OEMs) typically use over-the-air updates to deploy firmware and configure phones for use on their networks over Wi-Fi or mobile broadband. The initialization of a newly purchased phone, for example, requires an over-the-air update. With the rise of smartphones, tablets and internet of things (IoT) devices, carriers and manufacturers have turned to different over-the-air update architecture methods for deploying new OSes to these devices.
History of OTA updates
OTA technology has grown more prominent with the growth of mobile devices and applications. Mobile operators and telecommunication third parties can send OTA updates through SMS to configure data updates in SIM cards, distribute system updates, or access services such as wireless access protocol (WAP) or multimedia messaging service (MMS). OTA updates also enable mobile operators to activate user subscriptions. OEMs can use OTA updates to fix bugs through firmware and change the user interface.
The proliferation of IoT has led manufacturers to use OTA updates for autonomous vehicles, smart home speakers and other IoT devices. These manufacturers typically update their systems through unlicensed frequency bands, such as 868 MHz, and low data rate transmission protocols, such as 802.15.4.
Apple introduced OTA updates to iOS devices with the release of iOS 5.0.1. Previously, end users needed to connect the device to a computer using a USB cord and update the OS through iTunes. With OTA updates, however, Apple can deliver updates remotely in unencrypted zip files.
How OTA updates work
OEMs can deliver OTA updates to users in a few ways. From the end user's perspective, the OTA update can either be automatic or manual.
With an automatic OTA update, the back-end system of a mobile operator can push a firmware update to the end user's device. OEMs can use products that automate OTA updates, such as platforms from Smith Micro and Akamai, to manage and deploy OTA updates to their end users' devices. Devices that are in remote locations, such as IoT sensors, or devices that don't have frequent human contact, such as an autonomous vehicle, are good contenders for automatic OTA updates.
Manual OTA updates notify a user about an available update, and the user can accept or refuse to download the update on their device. Mobile carriers can also send an SMS message to all users who have a particular device, prompting them to dial a number to receive a software update when it is most convenient. For example, Verizon Wireless subscribers can dial *228 to either configure a 3G mobile device or update the preferred roaming list on the device.
IoT devices can receive OTA updates in a variety of ways. With edge-to-cloud OTA updates, a microcontroller receives firmware images from a remote server to update the underlying hardware or application. Gateway-to-cloud OTA updates use an internet-connected gateway that receives updates from a remote server to update the software app itself, the software app's host environment or the gateway's firmware.
What are the benefits and drawbacks of OTA updates?
OTA updates are a more efficient way for OEMs to fix bugs and update software than to manually upgrade each individual device. OTA updates can catch issues before devices launch, which can save OEMs time and money, as well as reduce the software development and quality-assurance (QA) process. OTA updates also enable OEMs to update software more easily on devices that are difficult to access, such as advertising displays.
An OTA update is also convenient for end users because it prevents them from having to go to a physical store or connect to a PC to update their devices. Instead, the end user only needs to press a button on their smartphone to download a software update, for example.
There are some security risks involved with OTA updates. OEMs that don't properly secure their OTA update process can enable hackers to change the device's software. Attackers can push unofficial updates that introduce security vulnerabilities. For example, an OTA company called Adups gained notoriety in 2016 for installing adware and spyware to collect personal information from devices.
To avoid security breaches, OEMs should encrypt and authenticate OTA updates and deliver them to end users via a secure protocol.






